Conti is a type of Ransomware-as-a-Service (RaaS) modeled group that first appeared in early 2020. Like other ransomware groups, Conti typically operates by infiltrating a victim’s computer network, encrypting their data, and then demanding a ransom payment in exchange for the decryption key.
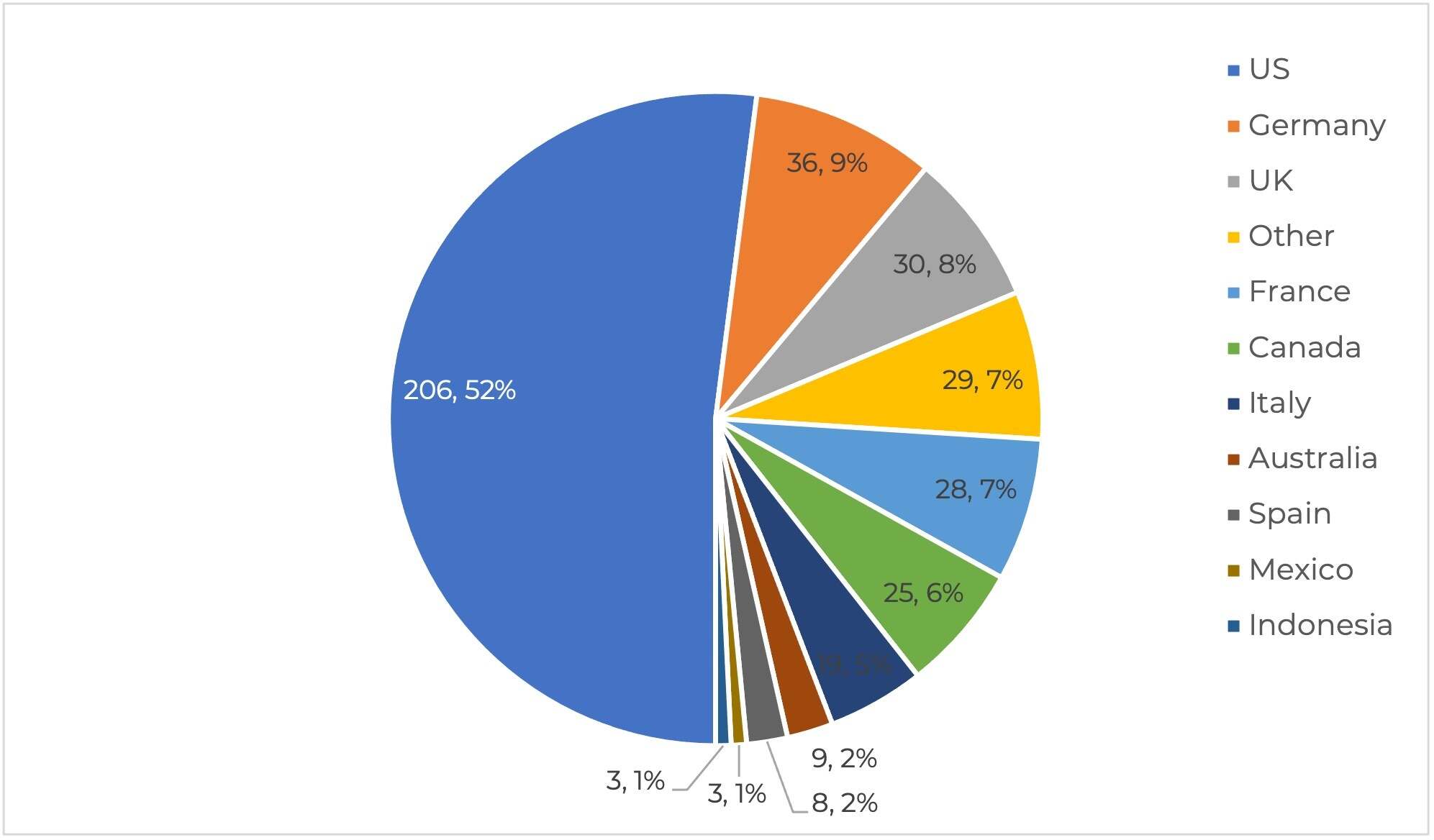
Conti ransomware has been responsible for several high-profile attacks on organizations around the world.
Where is Conti ransomware group from?
The origins of the Conti ransomware group are not definitively known, as the group operates anonymously and uses various techniques to conceal their identity and location. However, cybersecurity researchers have identified some possible links to other cybercriminal groups and regions based on the tactics, techniques, and procedures used by the group.
Some researchers have suggested that the Conti group may be associated with or have ties to cybercriminal groups based in Russia or Eastern Europe, based on factors such as the language used in ransom notes and the group’s targeting of organizations in those regions. However, it is important to note that these are only speculative theories, and the true origins of the group have not been definitively established.
It’s worth noting that ransomware attacks are often carried out by groups that operate across borders and use various tactics to conceal their identity and location. Regardless of the specific origin of the Conti group, the threat of ransomware is a global one, and organizations should take steps to protect their systems and data from potential attacks, regardless of where the attackers may be located.
Who is responsible for Conti ransomware?
The people responsible for the Conti ransomware group are not known with certainty, as the group operates anonymously and uses various techniques to hide their tracks. It is widely believed, however, that the group operates as a “ransomware-as-a-service” (RaaS) model, in which the ransomware is developed and sold to other cybercriminals who use it to carry out attacks.
In a RaaS model, the developers of the ransomware typically take a cut of any ransom payments made, while the actual attackers who carry out the attacks keep the bulk of the ransom payment. This model allows the developers to make money without directly carrying out the attacks, while also allowing the attackers to use sophisticated ransomware without having to develop it themselves.
There have been some reports suggesting that the Conti group may have links to other cybercriminal groups, but these reports have not been confirmed. It is also worth noting that the people responsible for the Conti group may operate under different names or affiliations, making it difficult to identify them with certainty. Regardless of who is behind the Conti group, the attacks carried out by the group can have significant consequences for the organizations and individuals who are targeted, highlighting the need for strong cybersecurity measures and preparedness against ransomware attacks.
Which are Conti Ransomware Most Famous Attacks?
Here are five most notable attacks attributed to the Conti ransomware group:
- Irish Health Service Executive (HSE): In May 2021, the Conti group attacked Ireland’s national healthcare system, causing widespread disruption and forcing the HSE to shut down many of its IT systems. The attackers demanded a ransom of $20 million in exchange for the decryption key.
- AXA Group: In June 2021, the French insurance company AXA Group suffered a ransomware attack by the Conti group, which resulted in the theft of sensitive customer data. The group demanded a ransom of $300 million in exchange for the data and threatened to release the data if the ransom was not paid.
- University of Utah: In July 2020, the Conti group targeted the University of Utah and demanded a ransom of $457,059 in exchange for the decryption key. The attack disrupted the university’s computer systems, including email and online coursework, causing significant disruption to students and faculty.
- Brown-Forman: In June 2020, the Conti group targeted the American alcohol company Brown-Forman, the maker of Jack Daniel’s whiskey. The attackers demanded a ransom of $1.5 million in exchange for the decryption key.
- City of Tulsa: In May 2021, the Conti group targeted the City of Tulsa, Oklahoma, and demanded a ransom of $7.5 million in exchange for the decryption key. The attack disrupted the city’s computer systems, including email and online services, causing significant disruption to city operations.
It’s important to note that the Conti group may have targeted other organizations as well, and the above list is not exhaustive. Ransomware attacks can have significant consequences for organizations, including loss of sensitive data, reputational damage, and financial losses. Organizations should take steps to protect their systems and data from ransomware attacks, including implementing strong cybersecurity practices and regularly backing up critical data.
Here is a general overview of how the Conti ransomware group works:
The Conti group is known for its sophisticated and targeted attacks, which can cause significant disruption to organizations and their operations.
Step #1: Initial infection
The Conti group typically gains access to a victim’s computer network by exploiting vulnerabilities in software or by using phishing attacks to trick users into downloading malware.
Step #2: Network reconnaissance
Once the group gains access to a victim’s network, they will typically spend time performing reconnaissance to identify key systems, data, and users to target for encryption.
Step #3: Data encryption
After identifying the most valuable targets, the group will deploy their ransomware to encrypt the data on those systems, making it inaccessible to the victim.
Step #4: Ransom demand
Once the data is encrypted, the Conti group will typically demand a ransom payment in exchange for the decryption key. The ransom demand may be communicated through a ransom note left on the victim’s system or through direct communication with the victim via email or other means.
Step #5: Pressure and extortion
In some cases, the Conti group has been known to pressure victims to pay the ransom by threatening to leak sensitive data that they have stolen from the victim’s network during the initial infection.
It’s worth noting that every ransomware attack is different, and the Conti group may use variations of the tactics described above in different attacks. To protect against Conti and other ransomware groups, it’s important to implement strong cybersecurity practices, including keeping software up to date, training users on how to avoid phishing attacks, and implementing regular backups of critical data.
Methods Used by Conti Ransomware to Infiltrate Systems
Conti ransomware employs a multi-faceted approach to infiltrate systems, leveraging a combination of social engineering, exploitation of vulnerabilities, RDP exploitation, and the use of initial access malware. Once inside the network, Conti operators focus on privilege escalation, lateral movement, and maintaining persistent access through backdoors. The final stages involve data exfiltration and double extortion, making Conti one of the most sophisticated and dangerous ransomware threats in the cyber threat landscape.
Technical Breakdown: Methods Used by Conti Ransomware to Infiltrate Systems
Conti ransomware is a highly sophisticated malware that employs a variety of methods to infiltrate systems. These methods are designed to exploit human vulnerabilities, software weaknesses, and network misconfigurations. Below is a detailed technical breakdown of the typical methods used by Conti ransomware to gain initial access to systems.
Phishing and Spearphishing Campaigns
Phishing and spearphishing are among the most common initial attack vectors used by Conti ransomware:
- Phishing Emails: These emails contain malicious attachments or links. When a user opens the attachment or clicks the link, malware is downloaded onto their device. The attachments often contain embedded scripts that execute upon opening, downloading secondary malware such as TrickBot or BazarLoader, which are used to establish a foothold in the network.
- Spearphishing: This is a more targeted form of phishing where emails are tailored to specific individuals or organizations. The emails appear to come from trusted sources, increasing the likelihood that the recipient will open the attachment or click the link.
Exploitation of Vulnerabilities
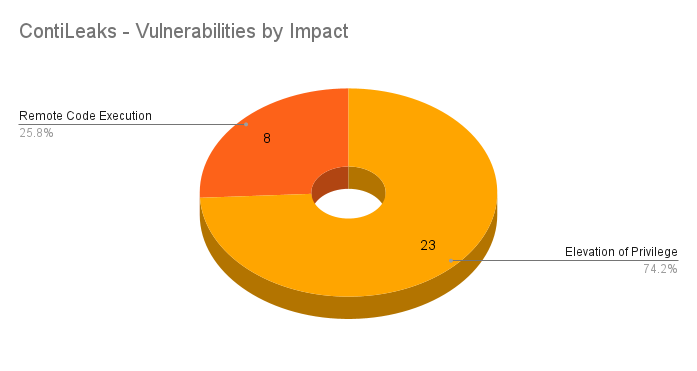
Conti ransomware exploits various software vulnerabilities to gain access to systems:
- Unpatched CVEs: Conti operators exploit known vulnerabilities in software and operating systems that have not been patched. This includes vulnerabilities in commonly used applications and services. For example, the Log4Shell vulnerability in the Apache Log4j framework was exploited by Conti to infiltrate systems and move laterally within networks.
- Vulnerable Firewalls: Weaknesses in firewall configurations are exploited to gain unauthorized access to internal networks. This often involves exploiting misconfigurations or outdated firewall software.
Remote Desktop Protocol (RDP) Exploitation
RDP exploitation is another common method used by Conti ransomware:
- Stolen or Weak RDP Credentials: Conti operators use stolen or weak RDP credentials to gain direct access to an organization’s devices. This method bypasses external defenses and allows attackers to control the compromised device remotely.
- Brute Force Attacks: Automated tools are used to perform brute force attacks on RDP endpoints, attempting various combinations of usernames and passwords until the correct credentials are found.
Purchasing Access from Network Access Brokers
Conti ransomware operators sometimes buy access to networks from other cybercriminals who have already compromised the target:
- Network Access Brokers: These brokers sell access to networks that have been previously breached. This allows Conti operators to skip the initial infiltration phase and move directly to lateral movement and data exfiltration.
5. Use of Initial Access Malware
Conti ransomware often uses initial access malware to establish a foothold in the target network:
- TrickBot and BazarLoader: These malware variants are commonly used to gain initial access. They are typically delivered via phishing emails and are responsible for downloading and executing additional payloads, including the Conti ransomware itself.
Exploiting Internet-Facing Services
Internet-facing services are often targeted to gain initial access:
- Internet-Facing RDP Servers: RDP servers exposed to the internet are prime targets for exploitation. Attackers use various techniques to gain access, including exploiting weak credentials and known vulnerabilities.
- Exploiting Web Applications: Vulnerabilities in web applications and services are exploited to gain unauthorized access to internal networks. This includes SQL injection, cross-site scripting (XSS), and other common web application vulnerabilities.
Privilege Escalation and Lateral Movement
Once initial access is gained, Conti operators focus on escalating privileges and moving laterally within the network:
- Credential Dumping: Tools like Mimikatz are used to dump credentials from memory. These credentials are then used to escalate privileges and gain access to additional systems within the network.
- Lateral Movement Tools: Conti uses tools like Cobalt Strike, AdFind, and PowerSploit to move laterally. These tools help identify and exploit network vulnerabilities, allowing the ransomware to spread to other devices.
Installation of Backdoors
To maintain persistent access, Conti operators install backdoors on compromised systems:
- Backdoor Malware: Backdoors like Cobalt Strike beacons and AnyDesk are installed to allow remote access and control. These backdoors enable attackers to re-enter the network at will, facilitating continuous monitoring and further exploitation.
- Command-and-Control (C2) Communication: The backdoors establish communication with Conti’s C2 servers, allowing attackers to issue commands and download additional tools and payloads.
Data Exfiltration and Double Extortion
Before encrypting files, Conti operators exfiltrate sensitive data:
- Data Exfiltration Tools: Tools like Rclone are used to upload exfiltrated data to cloud storage services controlled by the attackers. This data is then used for double extortion, where victims are threatened with the public release of their data if the ransom is not paid[4][5].
- Double Extortion: This tactic increases the pressure on victims to pay the ransom, as the public release of sensitive data can cause significant reputational and financial damage.
How does Conti ransomware spread to other devices on a network?
Conti ransomware employs several methods to spread across a network, leveraging both manual and automated techniques:
- Lateral Movement: Once initial access is gained, Conti uses tools like Cobalt Strike, AdFind, and PowerSploit to move laterally within the network. These tools help the attackers identify and exploit network vulnerabilities, allowing them to spread the ransomware to other devices.
- Server Message Block (SMB) Exploitation: Conti can spread via SMB, a network file-sharing protocol. By exploiting SMB, the ransomware can access and encrypt files on other endpoints within the same network domain.
- Credential Theft and Brute Force Attacks: Conti uses tools like Mimikatz to steal credentials and perform brute force attacks to gain access to additional systems. Once inside, it can use these credentials to move laterally and infect other devices.
- Backdoors and Persistence Mechanisms: Conti installs backdoors to maintain persistent access to the network. These backdoors allow the attackers to re-enter the network at will, facilitating further spread and data exfiltration.
How does the double extortion technique used by Conti work?
The double extortion technique employed by Conti involves two main stages:
- Data Encryption: Once Conti gains access to the network, it encrypts the victim’s data using AES-256 encryption. This makes the data inaccessible to the victim until a ransom is paid.
- Data Exfiltration and Extortion: Before encrypting the data, Conti exfiltrates sensitive information to servers controlled by the attackers. The attackers then threaten to release this data publicly if the ransom is not paid. This adds additional pressure on the victim to pay the ransom, as the public release of sensitive data can cause significant reputational and financial damage.
Conti Ransomware Indicators of Compromise (IoCs)
Indicators of Compromise (IoCs) are critical for identifying and mitigating threats posed by Conti ransomware. These IoCs include various artifacts such as domain names, IP addresses, file hashes, and specific behaviors associated with the ransomware. Below is a detailed breakdown of the IoCs associated with Conti ransomware:
Domains and IP Addresses
Conti ransomware uses a variety of domains and IP addresses to facilitate its operations. These domains often share similar lexical features and registration details, making them identifiable through WHOIS and IP analysis.
- Domains: Examples of domains used in Conti ransomware operations include
badiwaw[.]com,fipoleb[.]com,kipitep[.]com,pihafi[.]com, andtiyuzub[.]com[4]. These domains often follow a pattern of consonant-vowel sequences and may not resemble typical English words. - IP Addresses: Many of the domains resolve to IP addresses within specific ranges. For example, a significant portion of the domains resolve to IP addresses in the 23.0.0.0—23.255.255.255 range, which is assigned to Leaseweb USA, Inc.[2].
File Hashes
File hashes are unique identifiers for malicious files used by Conti ransomware. These hashes can be used to detect and block malicious files on networks and endpoints.
- Example Hash: One known file hash associated with Conti ransomware is
eae876886f19ba384f55778634a35a1d975414e83f22f6111e3e792f706301fe[8].
Tools and Payloads
Conti ransomware utilizes a variety of tools and payloads to execute its attacks. These tools are often legitimate software repurposed for malicious use.
- AdFind: A free Active Directory query tool used to gather information about the network.
- Mimikatz: A tool for credential dumping, specifically used to create memory dumps of the Local Security Authority Subsystem Service (LSASS) for later analysis and credential theft[1].
- Rclone: An open-source command-line program used to upload exfiltrated data to cloud storage services like MEGA[8].
Behavioral Indicators
Behavioral indicators are specific actions and patterns observed during Conti ransomware attacks.
- File and Directory Manipulation: Conti ransomware can enumerate through all open processes to search for any that have the string “sql” in their process name. It can also rapidly encrypt files using
CreateIoCompletionPort(),PostQueuedCompletionStatus(), andGetQueuedCompletionPort()functions[3]. - Service Stopping: Conti can stop up to 146 Windows services related to security, backup, database, and email solutions using the
net stopcommand[3]. - System Recovery Inhibition: Conti can delete Windows Volume Shadow Copies using the
vssadmincommand to inhibit system recovery[3].
Command and Control (C2) Infrastructure
Conti ransomware uses various methods to maintain communication with its command and control (C2) servers.
- Cobalt Strike: A penetration testing tool used to establish a C2 channel and gather information about domain admin accounts[8].
- AnyDesk and Atera: Remote access tools installed on target machines to maintain an open communication channel[8].
Leaked Tools and Techniques
Leaked internal documents and tools have provided additional insights into Conti’s operations.
- Encryption Tool: The Conti encryption tool has options for targeting specific paths, killing processes that interfere with file operations, and turning off VMware ESXi virtual machines[1].
- Credential Dumping Commands: Commands used for creating memory dumps of LSASS include:
rundll32.exe C:\windows\System32\comsvcs.dll, MiniDump PID C:\ProgramData\lsass.dmp full
wmic /node:[target] process call create "cmd /c rundll32.exe C:\windows\System32\comsvcs.dll, MiniDump PID C:\ProgramData\lsass.dmp full"
remote-exec psexec [target] cmd /c rundll32.exe C:\windows\System32\comsvcs.dll, MiniDump PID C:\ProgramData\lsass.dmp fullConclusion
Understanding and monitoring these IoCs can help organizations detect and mitigate Conti ransomware attacks. By analyzing domain patterns, IP addresses, file hashes, and specific behaviors, cybersecurity professionals can develop more effective defenses against this sophisticated threat. Regular updates and collaboration with threat intelligence sources are essential for staying ahead of Conti’s evolving tactics and techniques.
