Log4j (CVE-2021-44228, CVSSv3 10.0) is a critical vulnerability in the open-source Apache Log4j logging library framework.
Also known as Log4Shell, the RCE 0-day exploit found in log4j 2, a popular Java logging package, the vulnerability allows for unauthenticated remote code execution. Said another way- log4shell zero-day gives a hacker or an intruder the ability to run codes and attempt to gain access from your computer, which could result in theft or personal information logged against your privacy.
Log4j Vulnerability Explained in Simple Terms
Cyber security vendors were quick to take action when Log4j2, a critical security vulnerability, was exposed this month. It impacts the Apache Log4j library, which is used by many vital pieces of internet infrastructure.
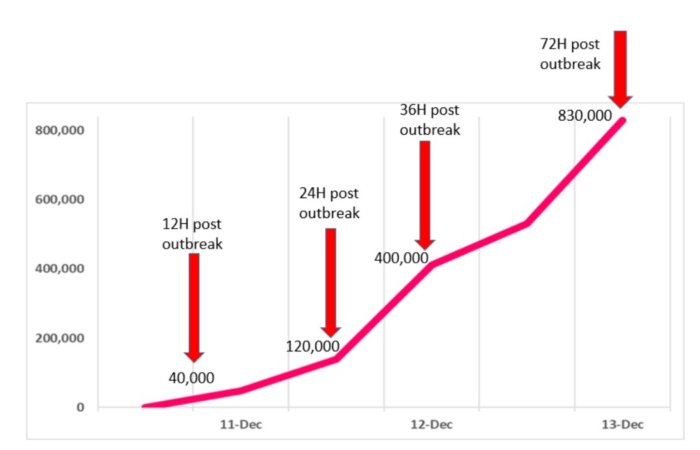
A highly critical remote code execution (RCE) security vulnerability was found, on December 9th, in the Apache logging package Log4j 2 versions 2.14.1 and below (CVE-2021-44228). A detailed description of the security vulnerability can be found at https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-44228.
The Apache team gave the log4shell vulnerability a severity score of 10 out of 10.
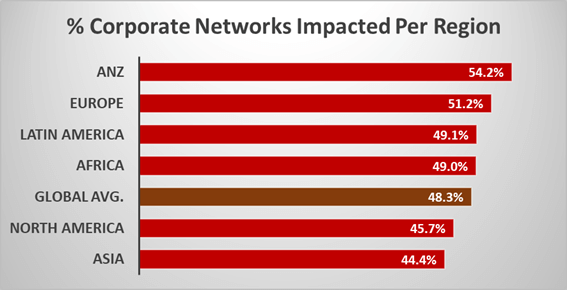
The newly discovered Zero-Day Flaw named Log4Shell is thought to be one of the worst flaws in cyber security history. Malicious threat actors and security hackers have used the Apache Log4j flaw to target more than 40% of corporate networks worldwide.
Critical security vulnerabilities in popular software such as the Apache Log4j library have become such a frequent occurrence that the cyber security community has started referring to issues such as these as “LogJams”.
These kinds of cyber-attacks are becoming more common than initially anticipated and is one of the many reasons why it’s so important for businesses to ensure vulnerability tests are being carried out on systems which could be impacted by potential flaws.
What is Log4J?
Log4j is an open-source java logging library created by the Apache Software Foundation. Although it runs across multiple operating systems including Windows, Linux, and macOS , it’s probably most known for its Java application as a logging utility which dates back to 1999.
The Apache Log4j library is an open-source tool that allows Java developers to produce detailed and configurable Java-based logs.
In other words, when you’re writing a piece of code, it’s important to remember that if there is an error (or “bug”) in the code, there is the potential for it to get amplified the more that you use your application. Therefore, having a tool by which you can monitor your computer networks and applications for such occurrences or so-called “bugs” can help save you and your customers from disastrous consequences.
Log4j is an open source tool that you can use for logging events in your programming apps. Its intended purposes are to make software construction easier and faster, give insight into problems and provide data for improved debugging.
And the Log4j library is used by almost everyone.
We’ve seen it in our own business, Twitter, Amazon and Microsoft. The Minecraft creators also use it. Among other companies too (most of which we’re not familiar with!).
“My view is we are going to see widespread exploitation by all manner of threat actors, and likely impacts on both public and private infrastructure. We’re doing everything we can with our partners to get ahead of that.”
Jen Easterly, Director of the Cybersecurity and Infrastructure Security Agency (CISA)
What is the Log4j, or “Log4Shell,” vulnerability?
What Is Log4Shell exploit? The Log4j CVE-2021-44228 Critical Vulnerability Explained
The Log4Shell security vulnerability, also known as CVE-2021-4428, affects the core functionality of Apache Log4j framework.
The Logj42 security vulnerability can be used to remotely execute code on a target computer’s operating system. On top of this, hackers can also run any code of their choosing as well as decline using other options to install ransomware or spyware onto devices if they wish to do so.
What is the impact of Apache Log4j Vulnerability?
Over 35,000 applications and tools that implement Java are vulnerable to the newly located Log4shell vulnerabilities.

The Log J4.2 security vulnerability could hack the reliability of entire e-commerce sites during the Christmas holidays and shut them down.
According to security experts, companies around the globe are at risk of being exposed if they use it. The bug could allow cybercriminals to gain access to any company’s sensitive data at will and could potentially cripple economic operations on a global scale.
According to Google, 35,863 Java artifacts in Maven Central may be vulnerable as of December 16, 2021.
Renowned as one of the most serious vulnerabilities online, hackers have exploited Log4j’s security vulnerability to compromise more than 40% of corporate networks worldwide.
Which are the affected Apache log4j versions?
log4j v2
log4j v1
CVE-2021-44228 Detail
How log4j vulnerability was found?
A researcher named Chen Zhaojun at Alibaba Cloud first reported the vulnerability to the Apache Software Foundation.
When Apache Foundation was nearly ready to patch the Logjam security flaw, Chen alerted the foundation that users on Chinese chat forums were speculating what possible exploits might involve this vulnerability and if hackers could pose any sort of threat right now.
How are hackers exploiting Log4Shell exploit?
Microsoft’s blog has been updated to reveal that as per the latest disclosures, hackers from China, Iran, North Korea, and Turkey have tried to exploit the Log4j security vulnerability.
A known Iranian hacking group, allegedly sponsored by the Islamic Revolutionary Guard Corps called APT 35 (aka “CharmingKitty”) has attempted to leverage the Log4j security vulnerability against seven Israeli targets across the government and business sectors. In the past, the hackers seemingly leveraged several spear-phishing emails containing malicious Microsoft Excel attachments that exploited CVE-2017-9805 (an Apache/Log4j flaw) for their malware payload (TrojanDownloader:Win32/Filecoder.A!cl).
Hacker groups are continuing to attempt various attempts at spreading ransomware to businesses. So far, the worst variants include Quantam, Kimsuky, Muhstik, Cerber and Black Sun.
What are log4j vulnerability mitigation solutions?
CISA recommends that in the first step, you should look for servers where a Log4j application is running and then upgrade them to version 2.15.0.
Log4j Vulnerability Remediation
Install the latest version of Log4j Library
Get Log4j Rapid Vulnerability Assessment
Detecting Malicious Behavioural Activities
Get Log4j Vulnerability Scanner
Vendors Response to log4j vulnerability
- Cloudflare rolling out mitigations for all customers, even free customers w/o WAF
- Google Cloud Armor WAF
- Imperva
