What is SaaS (Software as a Service)? – Definition and Key Concepts
Before we talk about SAAS security, it might be helpful for some of us to refresh our knowledge about what SAAS is. In simple terms, SAAS is an abbreviated form of Software-as-a-Service, which is a method of software delivery over the Internet.
Worldwide end-user spending on public cloud services is forecast to grow 18.4 percent in 2021.
[Source: Gartner]
In other words, SAAS is a cloud based software distribution method which is subscription based in nature. Users can subscribe to such apps and access a SAAS application from any compatible device over the internet.

What is ‘As A Service’ Meaning in SAAS?
Traditionally software developers have been presenting their work as ‘products’. With the advent of the SAAS delivery model, there is a sea change in how software is delivered and maintained.
Closest analogy is car parking. We see two kinds of options in the form of:
- valet parking
- renting a parking lot
If we liken car parking to the Cloud, we understand the difference of hosting and renting space. A cloud provider takes care of databases and codes needed as it provides you its own space for your software product.
As per the National Institute of Standards and Technology (NIST) suggestion, there are different types of ‘as a service’ technologies like:
- Self-service Cloud computing
- Paid on-demand
- Elastic
- Scalable
- Application Programming Interface accessible (APIs)
- Available over the internet


Non-SAAS Application – App’s logic runs on a user’s computer
SAAS Application – App’s logic runs on the Cloud
3 Layers of SaaS Architecture
Platform Infrastructure
= Servers, Networks and databases etc.
Cloud Network Topology
- Ethernet
- wireless
- TCP/IP protocols
- routing,
- VPNs
- VLANs
- Hybrid and SD-WANs and
- Compliance standards
- the OSI reference model etc.
Software
Growing Cloud Adoption Trends
In today’s SaaS (software as a service )market, where SaaS providers utilize highly secure public cloud services to deploy and store their software instances, it goes without saying that security of user privacy and corporate data is a dual responsibility.
Security of SaaS applications starts with collaboration as remote work locations skyrocketing and that is why efficient cloud strategies go hand in hand with cloud security providers for your SaaS application.
What is SAAS Security ? Definition
With SAAS Security, what we mean is the practice of securing user access and data privacy in a Cloud-based software application.
Shared Security Model for Security in the Cloud
Any Best Practices related to Protection of SaaS Application cover both external threats (environmental and human), taken care by SAAS security provider while the customer also needs to keep track of any malicious activity
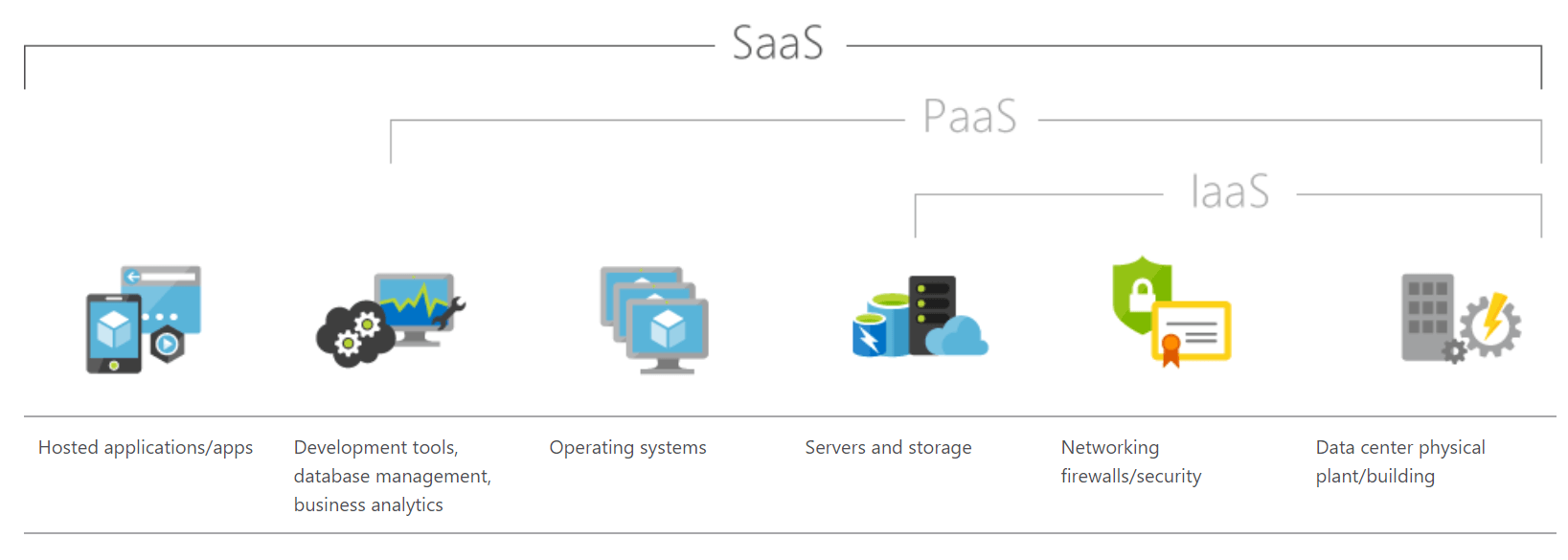
| On-Premises (for reference) | IaaS (Infrastructure as a Service) | PaaS (Platform as a Service) | SaaS (Software as a Service) |
| User Access | User Access | User Access | User Access |
| Data | Data | Data | Data |
| Applications | Applications | Applications | Applications |
| Operating System | Operating System | Operating System | Operating System |
| Network Traffic | Network Traffic | Network Traffic | Network Traffic |
| Hypervisor | Hypervisor | Hypervisor | Hypervisor |
| Infrastructure | Infrastructure | Infrastructure | Infrastructure |
| Physical | Physical | Physical | Physical |
Customer’s responsibility
Cloud Provider Responsibility
By 2023, the leading cloud service providers will have a distributed ATM-like presence to serve a subset of their services
Gartner
Top 10 Cloud Security threats
Cloud Security Threat #1: Data Breaches
: Reputational and financial, coupled with leakage of intellectual property (IP) and legal liabilities, are the direct outcomes of data breaches. Confidential information fell prey to major cloud data breaches like
- Capital One
- State Farm
- Equifax and
- Docker Hub etc.
are prime examples of how unauthorized individuals access cloud systems and creak havoc.
Cloud Security Threat #2: Cloud Misconfiguration of Resources
: The quest of making cloud data accessible and shareable at times leads to deployment of misconfigured resources; making vulnerable to malicious activity. This practice might look humane but when only 18% of businesses successfully detect and fix faulty configurations, the rest have no idea in hours (60%), days (20%), or months (2%).
In fact, cloud misconfigurations cost nearly $5 trillion
McAfee ‘Cloud-Native: The Infrastructure-as-a-Service (IaaS) Adoption and Risk Report‘ talks about this, specifically.
Cloud Security Threat #3: Lack of cloud security architecture
Growth in public cloud migration is staggering. It’s great but if types of users, amalgamation with third party vendors, policies and security coverage are put on the backburner, cloud security architecture and strategy goes for a toss.
We’ve seen two years of digital transformation in two months.
Microsoft’s CEO – Satya Nadella
Cloud Security Threat #4: Poor Identity, access, and key management
: Identity and access management system allows legitimate users, operators or developers access to manage, monitor and secure access to valuable resources. IAM’s role in the organization’s security stack leads to security breaches. Add poor multi-factor authentication and strong passwords, any hacker can get access to CIA.
Cloud Security Threat #5: Account hijacking
: Malicious cyber attackers have soft spot for account or service hijacking in cloud computing. In cloud environments, attempts in the form of
- Keyloggers
- Phishing
- Buffer overflow attacks
- Cross-Site Scripting (XSS) attacks
- Brute force attacks
etc. rob users of their account credentials.
Cloud Security Threat #6: Insider threat
:Cyber attacks do not take place from outside always. At times, malicious insiders like employees, former employees, contractors or business associates etc. abuses legitimate credentials. An alarmingly significant source of risk, such threats share valuable customer data, trade secrets in the aftermath of a cyber data breach.
Cloud Security Threat #7: Insecure interfaces and APIs
APIs are awesome but just. When Cloud service providers offer APIs to developers, to let them create interface, and interaction happens. This is the missing link where insecure API Cloud computing is seen as developers at times, create APIs without authentication. Result is common vulnerabilities and exposures (CVEs) and system Vulnerabilities are exposed in the open.
Cloud Security Threat #8: Weak Cloud Control Plane
If you are not given required arms in a battle ground, how would you react? SaaS security looks at weak cloud control plane when a customer is no provided the necessary security controls to keep security issues at bay. Missing two-factor authentication is an apt example of when it disables security and integrity.
