The open Web Application Security Project (OWASP) is a non-profit group whose mission is to make applications more secure. The rating system on the OWASP Top 10 has become standard for ranking web application security vulnerabilities and risks. The OWASP Top 10 provides rankings of—and remediation guidance for—the top 10 most critical web application security risks. Founded in 2001, the project has attracted a worldwide community of active and dedicated contributors to its cause.
The list is updated every three years and the latest version, the OWASP Top 10 2021, was released in April 2021.
What is OWASP Top 10 vulnerabilities list?
The OWASP Top 10 is a standard awareness document for developers and web application security. It represents a broad consensus about the most critical security risks to web applications. The OWASP Top 10 for 2021 was released in September 2021 and it lists the following 10 most critical web application security risks:
OWASP Top 10 Vulnerabilities 2021 List: A Closer Look
- OWASP A01 Broken Access Control
- OWASP A02 Cryptographic Failures
- OWASP A03 Injection
- OWASP A04 Insecure Design
- OWASP A05 Security Misconfiguration
- OWASP A06 Vulnerable and Outdated Components
- OWASP A07 Identification and Authentication Failures
- OWASP A08 Software and Data Integrity Failures
- OWASP A09 Security Logging and Monitoring Failures
- OWASP A10 Server Side Request Forgery (SSRF)
A01:2021 – Broken Access Control
What is the difference between Owasp 2017 and 2021?
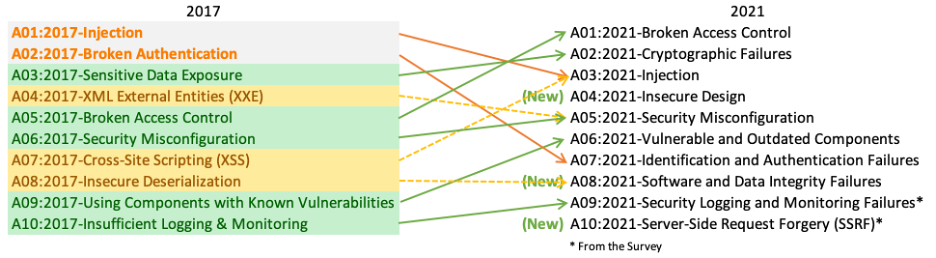
OWASP Top 10 Additions in 2021:
- Insecure Design (#4) was a new category added, highlighting risks from flaws in design and architecture.
- Software and Data Integrity Failures (#8) was also newly added, covering issues like unsigned libraries and insecure CI/CD pipelines.
- Server-Side Request Forgery (SSRF) (#10) was a new category covering SSRF vulnerabilities.
OWASP Top 10 Removals/Merges:
- The 2017 category “Unprotected APIs” was merged into the Broken Access Control category in 2021.
Reorganizations:
- Broken Authentication (2017) became Identification and Authentication Failures (#7) in 2021.
- XML External Entities (XXE) was merged from its own 2017 category into the Injection category (#3) in 2021.
Priority Changes:
- Injection moved down to #3 priority in 2021 from #1 in 2017.
- Broken Access Control became the new #1 priority in 2021.
The 2021 version also provided more details on vulnerability examples, testing guides, and coding best practices compared to 2017. Overall, it reflected an increased awareness of design flaws, software supply chain risks, and new vulnerability areas like SSRF.
Understanding OWASP Top 10 Security Vulnerabilities in 2024
A01:2021-Broken Access Control
Broken Access Control refers to situations where an application fails to properly enforce access restrictions, allowing users to act outside of their intended permissions. Access control enforces policies such that users cannot act outside of their intended permissions. Broken access control occurs when restrictions on what authenticated users are allowed to do are not properly enforced.
5 common examples of Broken Access Control vulnerabilities include:
- Bypassing access control checks by modifying object references like file names or database keys.
- Allowing unauthorized access to view or modify other users’ data and resources (horizontal privilege escalation).
- Granting users access to functionality or data that is unintended for their role (vertical privilege escalation).
- Missing access control checks on server-side processes that handle backend requests.
- Metadata manipulation vulnerabilities, such as modifying JSON Web Tokens without authorization.
- Forced browsing or URL/file path manipulation to access unauthorized resources.
How is broken access control exploited?
Attackers exploit these flaws to access unauthorized functionality or data, such as accessing other users’ accounts, viewing sensitive files, modifying other users’ data, and changing access rights, among others.
Here’s an example scenario of Broken Access Control:
Let’s say an e-commerce website has separate user roles like Customer, Staff, and Admin. Due to a Broken Access Control issue, a customer could modify URLs or parameters to gain access to staff interface pages, view orders of other customers, or even access admin functionality like modifying product prices.
What is broken access control vulnerability?
Broken Access Control, also known as A01:2021 in the OWASP Top 10 2021 list, is a vulnerability that occurs when an application lacks proper controls over who can access certain resources or perform certain actions. This can allow an attacker to gain unauthorized access to sensitive data or to perform actions that they should not be able to perform.
What causes broken access control vulnerability?
There are several ways that access control can be broken, including:
- Lack of proper authentication: If an application does not require strong authentication or does not verify the authenticity of users, an attacker may be able to gain access to restricted resources or perform unauthorized actions.
- Lack of proper authorization: If an application does not properly enforce access controls based on a user’s role or permissions, an attacker may be able to access resources or perform actions that they should not be able to access or perform.
- Insufficient session management: If an application does not properly manage user sessions, an attacker may be able to steal a user’s session and use it to access restricted resources or perform unauthorized actions.
- Lack of input validation: If an application does not properly validate user input, an attacker may be able to manipulate requests in order to gain unauthorized access to resources or to perform unauthorized actions.
Broken Access Control Mitigation Strategies
The impact of such vulnerabilities can be severe, as they may lead to data exposure, modification of data, unauthorized functionality access, or even full system/server compromise in some cases.
Here’s an example scenario: Let’s say an e-commerce website has separate user roles like Customer, Staff, and Admin. Due to a Broken Access Control issue, a customer could modify URLs or parameters to gain access to staff interface pages, view orders of other customers, or even access admin functionality like modifying product prices.
Mitigation techniques for Broken Access Control as per OWASP Top 10 2021:
- Deny by default – Implement access control mechanisms denying access to any resources by default.
- Principle of Least Privilege – Grant users only the permissions they need to perform their tasks, nothing more.
- Server-side access controls – Perform authorization checks on the server-side for every request.
- Avoid client-side access control – Client-side controls are easily bypassed and cannot be relied upon.
- Input validation – Validate and sanitize all user input to prevent modifications to object references.
- Segregate trust boundaries – Segregate application logic, libraries, and services based on trust levels.
- Centralize access control – Implement centralized components handling access control decisions.
- Log access control failures – Monitor and log failed access attempts which could indicate an attack.
By properly implementing access controls throughout the application, consistently validating inputs, segregating trust boundaries, and following the principle of least privilege, the risks from Broken Access Control vulnerabilities can be significantly reduced.
A02:2021 Cryptographic Failures
This refers to the failure in properly encrypting or protecting sensitive data, leading to potential exposure of personal, financial, or proprietary information.
How it works:
An attacker might intercept unencrypted data during transmission (e.g., man-in-the-middle attacks) or access unencrypted data stored on a server or database. This can result in data breaches, identity theft, and unauthorized access.
Mitigation Strategies:
- Utilize strong, up-to-date cryptographic standards for data at rest and in transit.
- Implement HTTPS with TLS for all connections.
- Securely store and manage encryption keys, keeping them separate from encrypted data.
- Regularly audit and update cryptographic practices to ensure compliance with current standards.
A03:2021 – Injection
Injection flaws occur when untrusted data sent to an interpreter is executed as a command or query, allowing attackers to manipulate backend logic.
How it works:
Common examples include SQL injection, where attackers manipulate database queries through unsafe user input, and command injection, where system commands are executed by the application.
Mitigation Strategies:
- Use prepared statements and parameterized queries to ensure database commands are safe from injection.
- Sanitize and validate all user input, especially data used in SQL, LDAP, XPath, or OS commands.
- Employ Object Relational Mapping (ORM) tools to abstract and secure database interactions.
- Implement allowlists for input validation to ensure only expected data is processed.
A04:2021 – Insecure Design
Insecure design encompasses vulnerabilities introduced through design flaws, often due to the absence of a systematic design process that incorporates security considerations.
How it works:
Design flaws can manifest in various ways, such as improper data isolation, insecure API endpoints, or the lack of proper authentication mechanisms. These flaws often provide attackers with avenues to exploit applications in unintended ways.
Mitigation Strategies:
- Integrate security into the design phase of the software development lifecycle, including the adoption of secure design principles and patterns.
- Conduct threat modeling for early identification and mitigation of potential design flaws.
- Ensure that design reviews and security testing are part of the development process.
- Provide training for developers on secure design practices and principles.
A05:2021 – Security Misconfiguration
This risk arises from improperly configured permissions, servers, frameworks, or security headers, leading to potentially exploitable vulnerabilities.
How it works:
Examples include unnecessary services running on a server, default accounts with unchanged passwords, or verbose error messages containing sensitive information. Attackers exploit these misconfigurations to gain unauthorized access or information.
Mitigation Strategies:
- Automate the process of configuring security settings to reduce the risk of human error.
- Regularly scan and audit systems for misconfigurations using automated tools.
- Implement a secure baseline configuration for all systems and continuously monitor for deviations.
Train developers and system administrators on the importance of secure configuration practices.
A06:2021 – Vulnerable and Outdated Components
This refers to using software components with known vulnerabilities, which can expose the application to attacks if these components are exploited.
How it works:
An attacker can exploit a vulnerability in a third-party library or component that the application depends on, potentially gaining unauthorized access or compromising the application’s integrity.
Mitigation Strategies:
- Regularly update and patch all libraries, frameworks, and components used by the application.
- Use software composition analysis tools to identify and track vulnerabilities in components.
- Remove unused dependencies and unnecessary features to minimize the attack surface.
- Establish a process for quickly responding to newly discovered vulnerabilities in components used by the application.
A07:2021 – Identification and Authentication Failures
This category focuses on weaknesses in authentication and session management mechanisms that could allow attackers to compromise passwords, tokens, or keys.
How it works:
Vulnerabilities might include weak password policies, insecure password recovery mechanisms, and improper session handling, allowing attackers to assume the identity of legitimate users.
Mitigation Strategies:
Implement multi-factor authentication to add an additional layer of security.
Secure password storage using modern, adaptive cryptographic algorithms like bcrypt.
Ensure secure session management practices, including secure generation and storage of session identifiers.
Monitor and log failed authentication attempts and establish mechanisms to detect and respond to brute force attacks.
A08:2021 – Software and Data Integrity Failures
This risk involves the lack of validation, improper use, or failure to secure the integrity of software and data, leading to unauthorized modifications or exploitation.
How it works:
An example is an attacker manipulating software update mechanisms to distribute malicious updates or tampering with data in transit.
Mitigation Strategies:
Ensure the integrity of software updates and data through digital signatures or similar mechanisms.
Use secure protocols for transmitting sensitive data to prevent man-in-the-middle attacks.
Implement mechanisms to detect and respond to unauthorized modifications of critical data.
Secure the supply chain to prevent the introduction of vulnerabilities through third-party components or services.
A09:2021 – Security Logging and Monitoring Failures
Insufficient logging and monitoring, combined with ineffective or absent integration with incident response, allow attackers to further exploit systems without detection.
How it works:
This could involve an attacker exploiting other vulnerabilities without detection due to lack of or inadequate logging of security-relevant events and insufficient monitoring for suspicious activities.
Mitigation Strategies:
- Implement comprehensive logging of security-relevant events and ensure logs are stored securely.
- Use automated tools to monitor logs and detect suspicious activities in real-time.
- Establish an incident response plan that includes procedures for responding to alerts generated by monitoring systems.
- Regularly test and audit the effectiveness of monitoring and logging mechanisms.
A10:2021 – Server-Side Request Forgery (SSRF)
SSRF occurs when an attacker can induce the server-side application to make HTTP requests to an arbitrary domain of their choosing, potentially accessing or manipulating internal resources.
How it works:
This can allow attackers to bypass firewalls and access internal services, such as metadata services in cloud environments, leading to information disclosure or internal system manipulation.
Mitigation Strategies:
- Validate and sanitize all user-supplied URL input to ensure only allowed domains and protocols are accessible.
- Employ network segmentation and firewall rules to limit the URLs to which the server can make requests.
- Disable HTTP redirections and limit outgoing server requests to only necessary endpoints and services.
- Regularly audit and test for SSRF vulnerabilities, including review of code and configuration settings that control external requests.
