Following a rapid increase in reported incidences of a new virulent strain of malware, security researchers have drawn up a list of the top 8 worst cyber-attacks that occurred in 2024.
8 of the biggest and latest cyber attacks of 2025
With several ransomware incidents and even a large scale attack on suppliers that resulted in the need for critical re-stocking, such statistics hammer home how important adequate cybersecurity measures are to any modern company looking to protect themselves from such threats!
Let’s take a look at the biggest cyber attacks of 2025
- T-Mobile Data Breach – January 2021
- Kroger Data Breach – February 2021
- California DMV Data Breach – February 2021
- Microsoft Exchange Server Data Breach – March 2021
- Colonial Pipeline Ransomware cyber attack – May 2021
- JBS Ransomware Attack – May 2021
- Phishing Attack on California State Controller’s Office – March 2021
- Facebook Data Leak/Breach – April 2021
Colonial Pipeline Ransomware cyber attack – May 2021
Let’s kick things off with what happened. Just last month, Colonial pipeline shut down.
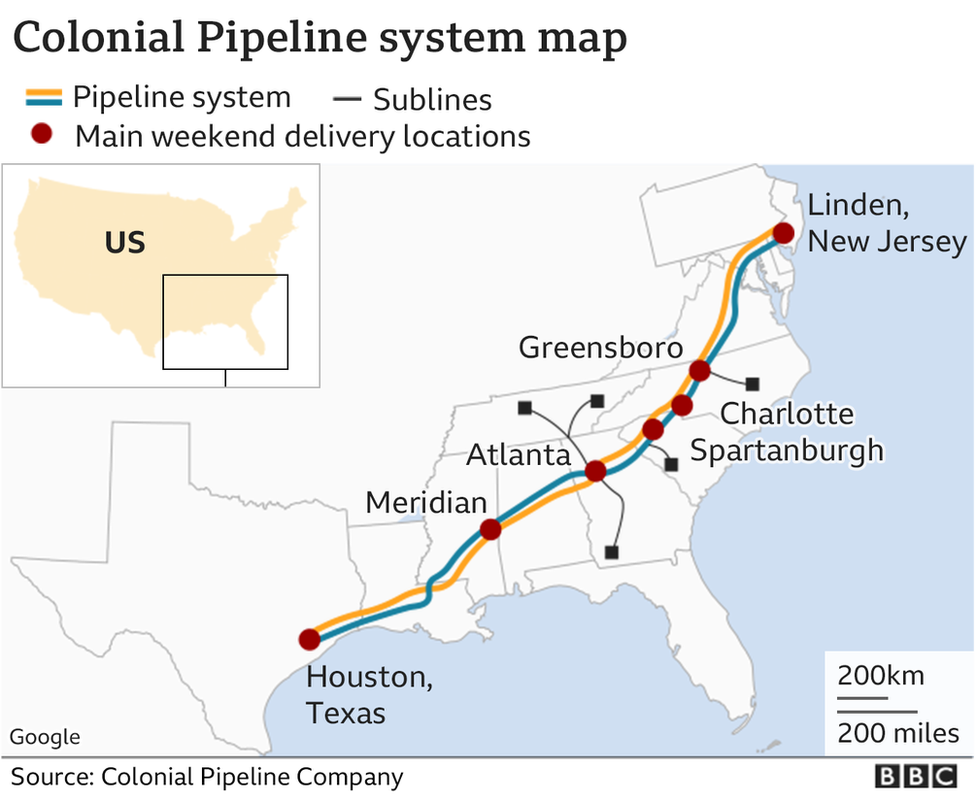
It’s 5500 miles of pipeline or 45% of the East Coast fuels buys an effort to contain a breach on its computer networks.
TL;DR
- What was affected? 5, 500 Miles of Pipeline
- What was cyber attacked? 100 GB of data
- Cause of Cyber attack – Ransomware-as-a-Service
- Impact – Operations were halted
Colonial Pipeline cyber attack Timeline
- May 6, 2021:
- May 7, 2021:
- May 8, 2021:
- May 9, 2021:
- May 10, 2021:
- May 11, 2021:
- May 12, 2021:
How did the hackers get into Colonial Pipeline?
So, how much is the ransom for colonial pipeline? The hacker stole nearly 100 gigabytes of data and threatened to leak it if the ransom wasn’t paid.
Colonial paid 4.4 million in Bitcoin, of which 2.3 million was eventually recovered by the FBI, how did the attackers gain access? They bought ransomware off the shelf marade somewhere.
Who was behind colonial pipeline cyber attack?
As a service provider known as dark side, the Dark Side Gang acquired the password to a single VPN account ,that was no longer in use, yet remained active.
The attackers gained access to the network through a single factor method.
Impact of Colonial Pipeline Cyber Attack
Colonial took down its systems, fearing that attackers may have obtained information from its computer networks that would enable them to attack susceptible parts of the pipeline.

Almost immediately, nervous drivers raced to gas stations in 11 states , which led to a fuel shortage in 12,000 different locations, many of which were completely sold out or nearly. Gas stations throughout the East coast reported running out of gas entirely, and drivers were offered only $3 per gallon, due to high demand – the highest level on the East coast in nearly 8 years.
How did Colonial pipeline respond?
They stopped all operations temporarily and they hired FireEye to investigate. If anything, Colonial pipeline is lucky they are so important to the functioning of the American economy.
Its systematic status helped to mobilize the full resources of the US government and even elicited other apology of sorts.
From dark side, the group issued a statement on the dark web saying “our goal is to make money and not creating problems for society.
From today we introduce moderation and check each company that our partners want to encrypt to avoid sense social consequences. “
There is so much more to this story. Brian Krebs, a popular security researcher and former Washington Post reporter did a deep dive on the dark side on the heady topic on his blog Krebs on Security, which is informative and interesting for anyone with an interest in technology or cybercrime
Ransomware as a services look like the folowing:

1st, If you can believe it, this gang has principles. Go figure. They’ve listed organizations. They will not attack, which is why they say the colonial pipeline attack was a mistake of sorts.
And going forward, they’ll get their partner targets more carefully.
Second, these guys are running a business as such.
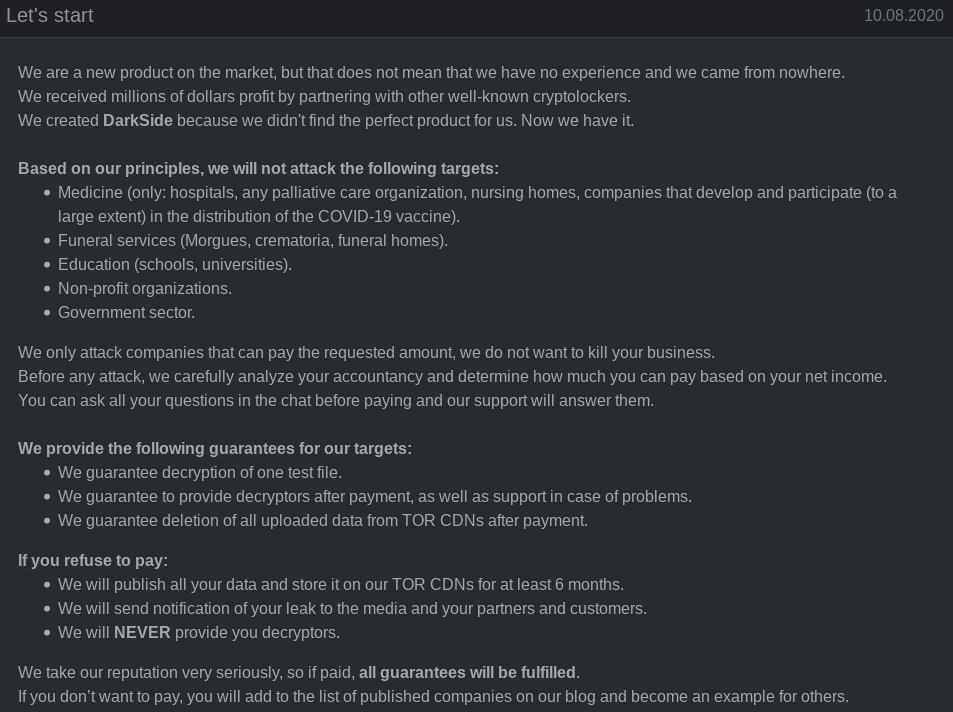
They have a well defined ideal customer profile. They only attack companies who have deep pockets and they know exactly how much they’re able to pay any ransom.
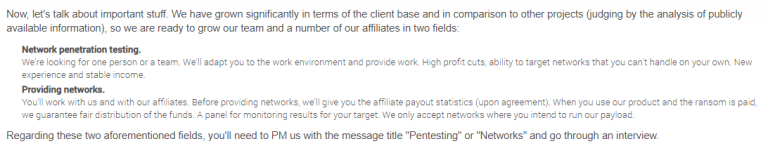
Check out this:
Further, they’ll answer any questions the victim company has in a chat.
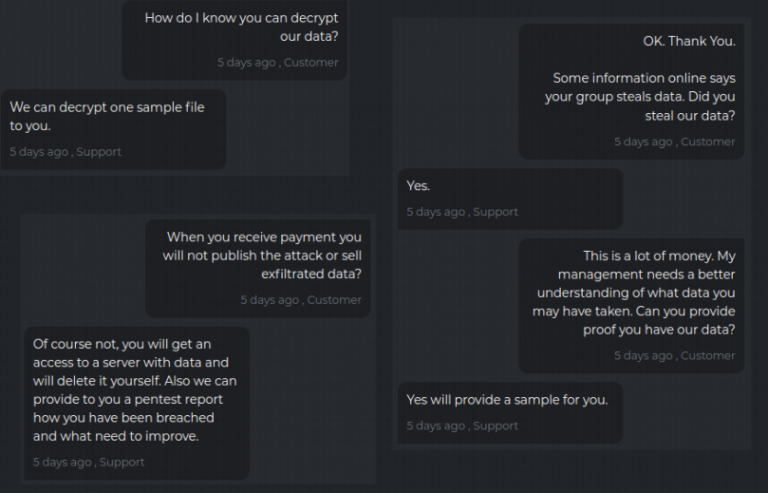
Dark Side also shares how they got into victim networks to gain access of security controls.
Weeks after Colonial ransomware cyber attack, JBS was cyber attacked when REvil used ransomware.
JBS Ransomware Attack – May 2021
Weeks after the incident with the Colonial Pipeline, Russia based cybercriminals used ransomware to gain access to JBS SA’s network, which resulted in extortion for money.
What information was taken? It’s not unknown what data was taken was exactly.
(adsbygoogle = window.adsbygoogle || []).push({});TL DR
- Who affected? Meat Supplier Processing
- What was under attack? Unknown
- Cause of Ransomware attack – Ransomware-as-a-Service
- Impact? Operations were halted
JBS Cyber attack timeline
- June 1, 2021: Threat actors encrypted the environment.
- March – May 2021: Data exfiltration from March 2021 to May 29, 2021.
- February 2021: Reconnaissance initiated
How did the attackers gain access?
Ransomware as a service. The FBI stated that REVil is one of the most specialized and sophisticated cyber promote groups in the world, with a reputation for attempting to extort far larger payments from its corporate victims and typically seen in other attacks. They threatened to publish the data if ransomware isn’t paid.
What was the impact of JBS Cyber attack?
Pretty significant.
- The cyber attack powered down the plant’s two shifts, and halted halted processing at one of Canada’s largest meatpacking plants.
- Nine beef plants in the United States were shut down
- poultry and pork plants were disrupted
- all this had said most significant effects on grocery stores and restaurants which would have charge more or remove meat products from their menus.
How did JBS respond?
JBS paid out an $11 million ransom. This is despite their resolution of issues related to security protocols, systems and encrypted backup servers.
This was a very difficult decision to make for our company and for me personally,” . “However, we felt this decision had to be made to prevent any potential risk for our customers
Andre Nogueira, Chief Executive Officer, JBS Foods statement
In January, T-Mobile reported a breach that compromised customer data.
T-Mobile Data Breach – January 2021
The company 4th in three years, the breach was thought to have impacted 200,000 users initially – which after a while turned out to 400.
- What affected? 200,000 / 400 years
- What was under cyber attack? PII (personally identifiable information)
- Cause of cyber attack – Compromised accounts
- Impact of data breach – SIM Swap Fraud
What information was taken?
- Customer personally identifiable information.
- Full names, addresses,
- account numbers
- Social Security numbers
- account pin numbers
- account security questions and answers and
- dates of birth.
This is all the data you need to fully steal someone’s identity.
How did the attackers gain access?
Either by compromising and employees account or users account.
It’s unclear whether the compromise accounts with the result of a massive data breach that happened last March or individual account takeovers resulting from week or reused passwords. Both are very typical and pretty poor.
What was the Impact of Incident?
Attackers stole phone numbers information to place them on other carriers.
SIM swap fraud or SIM hijacking allow scammers to take control of target phone numbers after porting them.
Once a number is ported, the attackers received the victims messages and calls. By stealing this valuable data, attackers were able to bypass SMS-based 2 factor authentication (2FA/MFA) on third party online service providers as well as compromise valuable accounts belonging to users. This card hijacking attack proves once again the importance of not only protecting valuable user data but also taking an approach that allows for different levels of intrusion detection, monitoring and alerting..
The criminals can then log into the victims bank accounts and steal their money.
They can change account passwords and even lock the victims out of their own accounts.
Pretty brutal.
How did T-Mobile mobile respond?
The company is offering two years’ worth of credit and identity monitoring through TransUnion’s My TrueIdentity service.
Kroger Data Breach – February 2021
In fact, so in February, Kroger reported a breach where customers were affected, specifically some using its health and money services, as well as current and former employees.
- Who affected? Customers and employees
- What was taken? Confidential PII
- Reason of data breach – Third Party File Xfer Service
- Impact? Federal Class-action lawsuit
Kroger has 2800 stores in 35 States and 500,000 employees. Approximately 2% of their customers were impacted and unknown number of employees.
Anyway you look at this, it’s a sizable breach.
What information was taken?
Names phone numbers,
dates of birth
Home address is medical history.
- Email addresses
- money, service records,
- Social Security numbers,
- prescription information and
- health insurance information.
This is all the data attackers need to steal someone’s identity.
Attackers could use the medical history, health insurance, and prescription information to commit targeted social engineering attacks on victims. These attacks make it even easier for attackers to harm their victims as doing so would provide them with more targeted pieces of sensitive information that could be used to compromise their identities.
How did The attackers gain access?
Here’s the sad part. This breach was totally avoidable. An unauthorized person gained access to certain.
Reason of Kroger Data Breach- Accellion Incident
Kroger files by exploiting a vulnerability in the Excellon network. The company formerly used a third party file transfer service called “Excellon” to get documents from one person to another over the internet.
Excellon had asked its customers late last year to switch over to a new product (since the 20 year old application program was using was nearing end of life.), so Kroger reported the vulnerability and filed its patent application for their free transportation system while Excellon still hadn’t patched the hole in their software by then end of this year.
Cooper did not upgrade and were breached via this third party app. What was the impact in March? A federal class action lawsuit was filed.
The lawsuit says program had full knowledge that excel in data security on the platform properties was LAX and they did it. Excellon had encouraged cover to move to a newer and more secure file transfer platform.
The lawsuit says program instead chose to use the outdated and unsecured transfer platform. Other companies have also been affected by the EXCELLON vulnerability. This data breach highlights the urgent need to replace legacy end of life tools.
And how did Kroger responds the company is offering victims yet again A2 year subscription to a credit monitoring service.
However, the lawsuit alleges that this arrangement is not sufficient because it will force employees and customers to pay for access to data they don’t own.
Out of pocket for credit monitoring for the rest of their lives.
Realize that.
California DMV Data Breach – February 2021
More recently, in February, California’s Department of Motor Vehicles affected over 338 million vehicle registration records.
TL; DR
- Who affected? 38 million records
- What was affected? Vehicle Reg data
- Reason of CA DMV data breach – Ransomware via 3rd party
- Impact- End 3rd party service
What information was taken, names, addresses, license plate numbers and vehicle identification numbers. This is information that could be used in highly.
Targeted spear phishing campaigns. How did the attackers gain access? A DMV contractor? An automatic funds transfer services was hit by ransomware.
The DMV has been using this contractor for verifying people change of addresses. The Cuba Reservoir group was likely to blame for the attack. A dark web site known to be used by the Cuban ransomware group. Listed automatic funds transfer as a victim, claiming the group stole financial documents.
Correspondence with back employees, account movements, balance sheets, and tax documents. Ransomware typically crypto companies files that will unlock them in exchange for ransom. But since many companies have.
Backups, some ransom, workgroups steal sensitive internal data and then threatened to publish it if unless that ransom is paid.
So what was the impact here? The DMV stopped all data transfers to automatic funds transfer services, and has since initiated an emergency contract with a different address verification company as.
Usually will usually with third party data breaches. The California DMV was not the only victim of this attack. A number of municipalities from different areas of the US have reported cases which were related to the same data breach.
To make things worse, MasterCard alerted banks to fraudulent charges, showing up on credit cards used to make purchases.
Through the DMV website from last August through January of this year, visa cards may also have been impacted, so there’s that.
How did the DMV respond?
They issued a statement saying they are looking at additional measures to bolster security, to protect information held by the DMV and companies they contract with.
Not the best.
So this one is a whopper.
Microsoft Exchange Server Data Breach – March 2021
According to a recent March publication of Bloomberg, there were four zero day vulnerabilities in Microsoft Exchange Server (CVE-2021-26855, CVE-2021-26857, CVE-2021-26858: CVSS 7.8, and CVE-2021-27065: CVSS 7.8) which are being actively exploited by state sponsored threat groups as well as those with less technological sophistication and more malicious intent and the number of attacks that emerged is still increasing. 60,000 organizations have been hacked as of March.
What information was taken?
This is a tough one to nail down because so many organizations were affected.
The experts are saying that if access is achieved, the explored vulnerabilities will allow threat actors to execute commands remotely, which can include uploading a web shell to establish persistence in the compromised systems. An adversary may utilize a web shell to steal data or execute additional malicious actions, such as downloading remote documents or network service scanning.
Sort actors often use compression utilities to compress and stage the stolen data for exfiltration. It’s a different. Groups have leveraged these vulnerabilities.
Post exploitation activities may vary depending on the actor behind the account, access to sensitive information system should be assumed to have occurred. Access to corporate emails could also lead to phishing attacks.
So how did they get a tax gain access to begin with? A Chinese government backed hacking group leveraged 40 day vulnerabilities on premise Microsoft Exchange Server.
So what’s been the impact?
Any organization running an on premise Exchange Server is most likely a victim of this.
The attack servers were so successful and so rapid that the attackers pure appear to have found a way to automate the process.
Microsoft issued explicit instructions for patching the security vulnerabilities, however, just because the fixes are applied does not mean backdoors would be ruled out.
The connection of these 4 vulnerabilities were evident when the company ran script on Github (including indicators of compromise).
A one click tool was introduced by the Redmond-based giant for business mitigation.
Microsoft has launched a one-click solution to mitigate its servers from being compromised by possible web shell attacks. In April, the US Department of Justice commented via their website that the Federal Bureau of Investigation had approval for legal authorization to remove web shells on Microsoft’s server running the Butterball software.
The risk to their Internet facing servers in April, the US Department of Justice said the FBI had a big court approval and authorization to remove web shells from Butterball exchange servers.
The firefighting activities involved hundreds of systems but did not include issuing patches or mitigations on behalf of the vendors.
So the entire situation is still unfolding and we won’t know the full impact for months.
How did Microsoft respond?
For fixation in scripts, Microsoft commercial users can enjoy on premise Microsoft Defender for Endpoint for good 3 months.
What we do really?
Yeah, it’s scary out there.
Phishing Attack on California State Controller’s Office – March 2021
TL; DR
- Who affected – 9, 000+ users
- What was taken? SSN, Sensitive Files
- Reason of cyber attack – Phishing
- Impact – More phishing emails
Also, in March, the California State Comptroller‘s Office was hit by a data breach.
The state controller acts as the chief financial officer of California, the 6th largest economy in the world. The state controller is to California what a baker is to a birthday cake: the chief financial officer and custodian of their 100 billion dollar economy! He or she also ensures that 9000 state workers are all well-taken care of.
He or she handles more than 100 billion dollars each year, and is responsible for managing a staff of 9000 employees while ensuring compensation and other benefits to be provided to state employees. As expected, over 9000 state workers were affected.
What information was taken, intruders told Social Security numbers and sensitive files on thousands of state workers.
How do they get access?
An employee in the state’s unclaimed property division became victim of a phishing email and ended up sharing his credentials with the hackers, unknowingly, providing an unauthorized user with access to their email account.
The unauthorized user had access to the account for 24 hours. The personal identifying information was compromised property holder reports.
What was the impact?
The intruder used the fishing, the Fish employees inbox to send targeted phishing emails to at least 9000 California State workers and their contacts.
That’s troublesome.
How did the state comptroller’s office respond?
They notified the employees contacts who may have received a potentially malicious email from the unauthorized user, and they urged those employees to place fraud alerts on their credit files for the major consumer bureaus.
Facebook Data Leak/Breach – April 2021
And finally, in April, the personal data of more than a half a billion Facebook users worldwide was leaked online for free in a hacker forum. Hackers really appreciate that what information was taken.
The leak includes:
- Personally identifiable information
- full names, emails
- phone numbers
- Facebook IDs
- Locations
- Birthdate and bio descriptions.
The exposed data belongs to Facebook users from 106 countries, including over 32 million records using the US 11 million users in the UK and 6 million users in India.
How did the attackers gain access to Facebook Data Breach ?
Malicious actors scraped the data by exploding abutre ability and now defunct feature on Facebook that allowed users to find each other by phone number. Facebook said it had found and fixed the issue in August of 2019.
So what was the impact?
It’s too soon to tell what this specific impact has been.
How do Facebook respond?
The company said it has no plans to notify users. On top of that, the company wasn’t sure which uses should they reach to inform about the incident.
Users of Facebook weighed the fact that the information was publicly available and that it was not an issue that users could fix themselves.
So, to find out whether your personal information was leaked in this breach, you can check the data tracking tool Have I been pawned its creator? Troy Hunt has upped and the site with the latest data.
From the largest cyberattack in history to the rise of ransomware, it’s been a busy year for cyberattacks. From August 1 through August 31, several major cyberattacks, data breaches and ransomware attacks happened. Make sure you’re aware of these major cyberattacks and data breaches. They might inspire you to protect your company’s assets.
Cyber-attacks, data breaches and Ransomware were a major problem in 2021, but they got even worse in 2022 and now they are the norm. This blog highlights some of the cyber-attacks that took place in August 2022.
Here’s a quick recap of the cyber-attack, data breaches, ransomware attacks and insider threats that hit businesses in August 2022.
- Recent Cyberattacks on aviation industry
- Recent Cyberattacks on power grid
- Recent Cyberattacks on critical infrastructure
- Recent Cyberattacks on healthcare
- Recent Cyberattacks on financial institutions
- Recent Cyberattacks on oil and gas companies
- Recent Cyberattacks on banks
- Recent Cyberattacks on energy infrastructure
- Recent Cyberattacks on hospitals
- Recent Cyberattacks on iot devices
- Recent Cyberattacks on manufacturing companies
- Recent Cyberattacks on power grid
- Recent Cyberattacks on pharmaceutical companies
- Recent Cyberattacks on retailers
- Recent Cyberattacks on US critical infrastructure
Recent Cyberattacks on aviation industry
- Ransomware attack on SpiceJet airline
- Cybersecurity data breach on SunWing Airlines Inc.
- Cyber attack on Russia’s Civil Aviation Authority servers
- cyberattack at SITA
- Ransomware attack on Top Aces
- Ransomware attack on Swissport
