Expert Virtual CISO Services for Enhanced Cybersecurity Posture
Secure Tomorrow,
with network of vCISO Service Providers for DSS Compliance Audit & Consulting
Do the following consequences of Operating Without a vCISO look familiar?
“We Survived a Ransomware Attack… But Barely”
Non-compliance can result in substantial financial penalties that vary depending on the severity of the non-compliance and the volume of transactions processed by the business. These fines are imposed by payment card companies and can range from $5,000 to $100,000 per month until compliance is achieved.
“Phishing Emails Keep Sneaking Past Our Defenses”
While PCI DSS itself is not a law, failure to comply can lead to legal actions due to breach of contractual obligations with payment card companies. Additionally, data breaches resulting from non-compliance could violate other national data protection regulations, leading to further legal consequences.
“Compliance Audits Feel Like a Minefield”
You just landed a dream client… until they asked for a SOC 2 report. Your team spent weeks scrambling to document controls, only to fail the audit because no one understood encryption standards. Now the deal’s on hold, and competitors are circling.
“Our IT Team Is Overwhelmed”
: A 5-person IT team juggles cybersecurity, network maintenance, and helpdesk requests. Burnout leads to overlooked patches, leaving the business exposed to exploits.
A Vendor’s Weak Security Became Our Problem”
A third-party payroll vendor suffers a breach, leaking your employees’ Social Security numbers. Your SMB faces lawsuits and must now audit all vendor contracts
vCISO As A Service aligned with your Budget Security Audits Policies Procedures 24/7 crisis management and vendor questionnaires & more.
Strategic Vision & Leadership
A vCISO develops and executes a cybersecurity roadmap tailored to the SMB’s goals, ensuring alignment with business objectives. This includes prioritizing initiatives like threat detection and compliance.
Access to senior-level expertise
Address talent shortage as vCISOs provide access to senior-level expertise without the need to hire full-time specialists, addressing the cybersecurity skills gap.
Proactive Risk Mitigation
vCISOs conduct vulnerability assessments, penetration testing, and threat modeling to identify weaknesses before attackers exploit them. This reduces breach risks by up to 60% and ensures compliance with frameworks like NIST or ISO 27001.
Compliance Made Simple
vCISOs translate complex regulations (GDPR, SOC 2, PCI-DSS) into actionable steps, avoiding costly fines and failed audits. They prepare documentation, train teams, and implement controls to turn compliance into a competitive advantage.
Strategic Roadmaps
vCISOs create 1-3 year cybersecurity plans aligned with business goals, ensuring investments target critical risks (e.g., securing customer data before a product launch). This avoids wasted spending on unnecessary tools.
Incident Response Preparedness
vCISOs develop breach playbooks, run tabletop exercises, and establish communication protocols to minimize downtime. Companies with a vCISO resolve incidents 50% faster, reducing average breach costs ($4.45M in 2023).
Vendor & Supply Chain Security
vCISOs assess third-party risks, enforce security requirements for vendors, and monitor supply chain threats. This prevents breaches caused by weak links, like a compromised SaaS provider.
Employee Training Programs
vCISOs design phishing simulations, security workshops, and policy training to reduce human error (the cause of 85% of breaches). Regular training cuts click rates on malicious emails by 40–60%.
Cyber Insurance Optimization
vCISOs help meet insurer requirements (e.g., MFA, backups), lowering premiums by 20–30%. They also ensure claims aren’t denied due to gaps in security controls.
Scalability
vCISO services grow with your business, whether you’re expanding to new markets, adopting cloud tools, or undergoing M&A. They adjust strategies to cover evolving risks without overburdening your team.
24/7 Threat Monitoring
Many vCISO providers include round-the-clock monitoring via SIEM tools or managed detection and response (MDR). This enables real-time alerts for suspicious activity, like unauthorized logins or data exfiltration.
Reputation Protection
By preventing breaches, vCISOs safeguard customer trust and avoid PR crises. 60% of SMBs close within 6 months of a major breach—vCISO services slash this risk.
vCISO FAQs To Know
What is a vCISO?
How does a vCISO differ from a traditional CISO?
How is a vCISO Different from a Traditional CISO?
Can a vCISO Replace an MSSP?
What services does a vCISO provide?
How does a vCISO handle incident response?
Have a question? Book a free 10-minutes call.
Choosing the right model depends on the SMB’s maturity, risk profile, and goals. For example, a startup might opt for on-demand support, while a scaling business benefits from a retainer.

Why gamble with DIY security? We blend brains (vCISO) and brawn (MSSP) to guard your growth
24/7 Threat Monitoring & Detection (MDR)
Continuously monitor networks, endpoints, and cloud environments for threats using tools like EDR, SIEM, and threat intelligence feeds. Also, proactively hunt for advanced threats (e.g., ransomware, zero-day exploits). The vCISO defines detection priorities (e.g., focus on phishing or supply chain risks), while MDR executes real-time monitoring.
Incident Response & Remediation
MSSPs contain breaches, eradicate threats, and restore systems during/after an attack. Includes forensic analysis and evidence preservation for legal/insurance needs.
Vulnerability Management
Scans for and patches vulnerabilities in software, firewalls, and cloud configurations. Prioritizes risks using CVSS scores and business impact analysis. The vCISO aligns patching schedules with business operations (e.g., avoid downtime during peak sales).
Endpoint Detection & Response (EDR)
Endpoint Detection & Response (EDR) What It Does: Deploys AI-driven tools (e.g., CrowdStrike, SentinelOne) to detect and block malware, phishing, and insider threats. Bundled with vCISO: The vCISO configures EDR policies (e.g., restrict USB access) and reviews alerts for strategic adjustments.
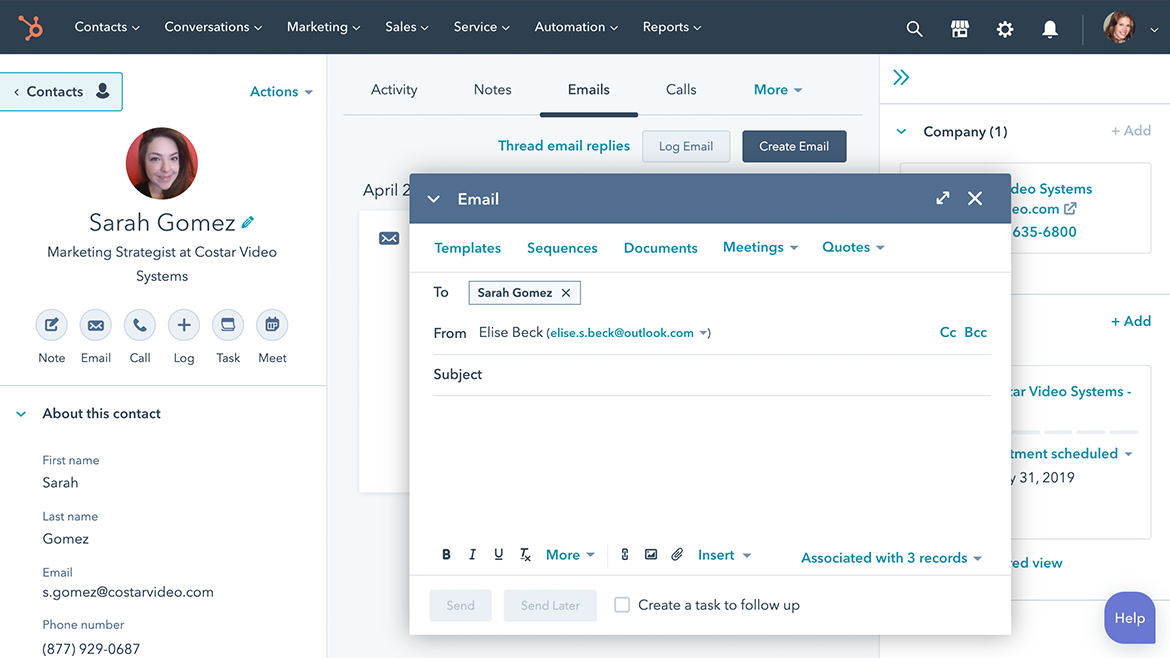
Compliance Monitoring & Reporting
Assistance with meeting regulatory requirements such as GDPR, HIPAA, or PCI-DSS. Preparation for audits through documentation, policy development, and control implementation.
Firewall and Intrusion Prevention System (IPS) Management
Configuration, monitoring, and maintenance of firewalls and IPS to protect against unauthorized access and network threats. Ensures optimal performance and up-to-date threat signatures.
Email and Web Security Services
Protection against phishing, malware, and other email-borne threats through filtering and threat intelligence. Web content filtering to prevent access to malicious or non-compliant websites.
Table-top exercises to ensure continuity of operations
Third-Party Risk Management
Evaluation and monitoring of vendors and partners to assess their security posture and potential risks. Implementation of controls to manage and mitigate third-party risks.
Security Audits & Assessments
Perform risk assessments
Implement governance
Evaluate vendor proposals
Real-Time Incident Response
Supercharge Inbound
Program/Policy Creation & Implementation
Remediation Assistance
External Audit Assistance
Penetration Testing
Vulnerability Assessments
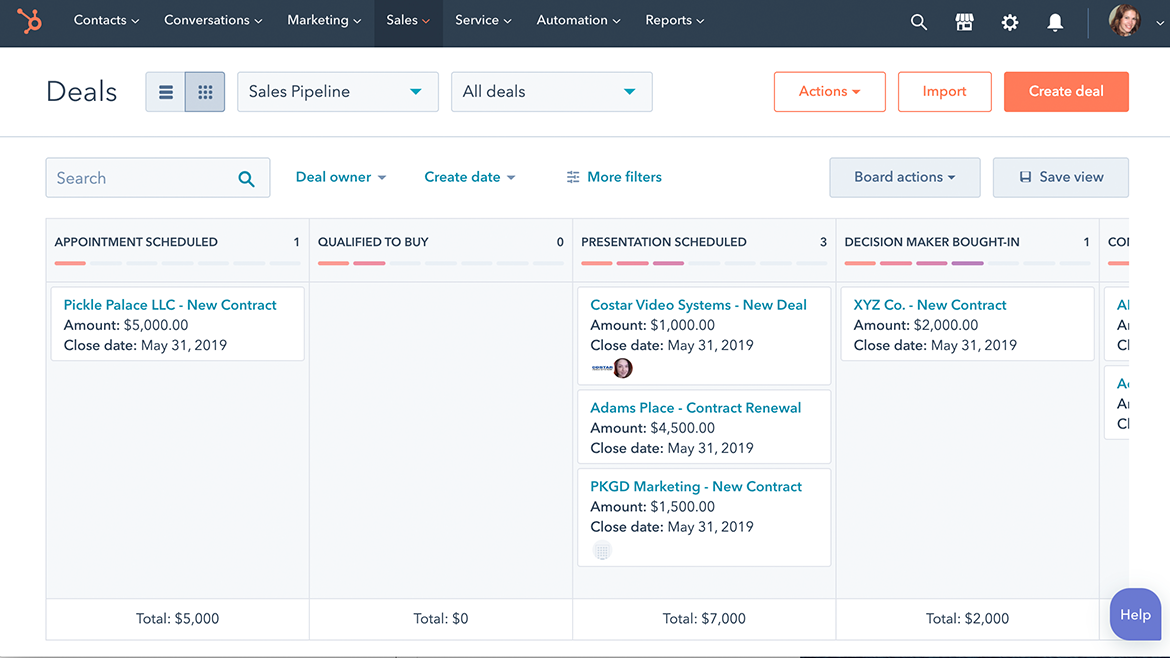
vCISO Service Engagement Models
By selecting the right vCISO engagement model, you can transform your organization's cybersecurity from a cost center into a strategic asset—ensuring resilience, compliance, and sustainable growth.
Project-Based vCISO Engagement
Focused on short-term goals (e.g., compliance audits, incident response planning, or risk assessments). A fixed monthly fee for ongoing, strategic cybersecurity leadership (typically 5–20 hours/month). Best for SMBs needing continuous guidance, compliance oversight, or risk management.
Retainer-Based vCISO Service Model
Ongoing support via a fixed monthly fee, covering regular strategy updates, monitoring, and advisory. A fixed monthly fee for ongoing, strategic cybersecurity leadership (typically 5–20 hours/month). Best for SMBs needing continuous guidance, compliance oversight, or risk management.
On-Demand (vCISO Advisory) Model
Pay-as-you-go services for ad-hoc needs (e.g., vendor risk assessments, breach consultations). Hourly or per-incident consulting for tactical needs (e.g., reviewing a vendor contract, responding to a breach). Best for SMBs with in-house IT teams needing occasional expert guidance.
Hybrid vCISO Service Model
Combines elements of retainer, project, and on-demand models to balance cost and coverage. Combines retainer-based support with project-based or on-demand services. Ideal for SMBs with fluctuating needs (e.g., seasonal businesses, rapid growth phases).
Fully Managed vCISO Service (Embedded Model)
The vCISO acts as an extension of your team, handling both strategy and execution. Includes coordinating with MSSPs, IT teams, and executives. Best for SMBs with no internal security staff.
Technology-Led vCISO Service Model
Bundles vCISO services with cybersecurity tools (e.g., EDR, SIEM, vulnerability scanners). The vCISO configures and oversees the tools, ensuring alignment with business goals.
Looking For Part-Time or Fractional vCISO Engagement For your SMB?
Talk to our vCISO Partners for ongoing strategic guidance provided on a part-time basis.