Virtual CISO (vCISO) Services: Bridging the Cybersecurity Gap for SMBs
Submit your information for a free session. Your financial goals are within reach – let's make them a reality together!
About us
SMB Cybersecurity Made Simple with Proven vCISO Services

Simplify Compliance and Security for SMBs with vCISO Expertise
cyber threats are no longer a distant concern for small and midsize businesses (SMBs)—they’re a daily reality. With 43% of cyberattacks targeting SMBs (Verizon DBIR 2023) and ransomware demands crippling businesses in minutes, cybersecurity has shifted from an IT checkbox to a boardroom imperative. Yet, SMBs face a daunting challenge: they lack the budget, expertise, or bandwidth to build enterprise-grade defenses.
Enter the Virtual Chief Information Security Officer (vCISO)—a strategic solution that delivers Fortune 500-level leadership at a fraction of the cost. Unlike traditional consultants or fragmented tools, a vCISO acts as your organization’s cybersecurity quarterback, combining strategic oversight with operational execution to transform vulnerabilities into business advantages.
Our services
Why SMBs Need a vCISO Now More Than Ever
Resource Constraints
SMBs need scalable, affordable expertise to avoid overspending on full-time roles
Outdated Technology
Legacy systems and unpatched software create entry points for attackers, but budget constraints hinder upgrades.
Vendor Management Risks
Overreliance on third-party vendors without vetting their security practices amplifies exposure to supply chain attacks.
Lack of Strategic Oversight
Without a CISO, SMBs struggle to align cybersecurity with business goals, prioritize investments, and integrate security into operational workflows.
Limited Expertise and Resources
Overworked IT teams lack specialized security skills, leading to misconfigured tools and poor threat detection. Many SMBs cannot afford advanced solutions or dedicated security staff.
Evolving Threat Landscape
Rapidly changing threats like ransomware and phishing require constant vigilance, but SMBs often lack the expertise to adapt defenses.
vCISO FAQs to Know
What is a vCISO?
Why does an organization need a vCISO?
What is the Difference Between vCISO, Fractional CISO, and CISOaaS?
- vCISO: Provides flexible, remote support for strategy, compliance, and risk management. Engaged on-demand or part-time.
- Fractional CISO: Dedicates set hours/days weekly to an organization, often for hands-on execution (e.g., policy drafting)
- CISOaaS (CISO-as-a-Service): A broader term encompassing both vCISO and fractional CISO models, often including operational tasks like incident response
.
What are the roles and responsibilities of the vCISO?
A vCISO’s responsibilities typically include:
Developing and implementing cybersecurity strategies aligned with business objectives.
RSI Security
Conducting risk assessments to identify and mitigate security threats.
Ensuring compliance with relevant regulations and standards.
Overseeing incident response planning and execution.
Providing security training and awareness programs for staff.
Advising on security architecture and technology investments.
Is vCISO a one-time project or an ongoing service?
What types of SMBs need a vCISO?
Who provides vCISO services?
How to choose a vCISO service provider for an SMB?
Data Breaches Don’t Discriminate
Phishing, Ransomware & More: The Top Threats Devastating SMBs
of all cyber attacks target SMBs annually
of ransomware attacks target companies with <1,000 employees
more social engineering attacks, experienced by employees than larger companies
more SMBs likely targeted than larger companies
Trusted vCISO service providers to translate technical risks into business impacts
Gain access to a network of vendor-neutral MSSPs, and consultancies that offer vCISO services.
Who Are We
We are a dedicated team of seasoned cybersecurity professionals committed to safeguarding small and medium-sized businesses (SMBs) across the United States. Recognizing the unique challenges that SMBs face in today’s digital landscape, we specialize in offering strategic leadership with operational execution, ensuring that your organization’s cybersecurity posture is robust, compliant, and resilient.
Our Mission: Empowering SMBs Through Curated vCISOs
We understand that each business operates within its own context, facing distinct threats and regulatory requirements.
Our vCISO + MSSP Partners
To deliver comprehensive and effective cybersecurity solutions, we collaborate with a network of esteemed Managed Security Service Providers (MSSPs). These partnerships allow us to extend our vCISO services, offering both strategic oversight and tactical support
Comparison between vCISO and CISO for SMBs
| Criteria | In-House CISO | Virtual CISO Service |
|---|---|---|
| Cost | High salary ($208k–$337k+) + benefits | 50–70% cheaper; hourly/project-based pricing |
| Expertise | Deep knowledge of company culture but limited to internal experience | Broader industry experience and access to niche skills (e.g., compliance frameworks) |
| Flexibility | Fixed role; scaling requires hiring more staff | On-demand engagement (e.g., part-time, retainer) |
| Scalability | Costly to scale; tied to headcount | Adapts to SMB needs (e.g., compliance audits, incident response) |
| Compliance | Manages compliance but may lack bandwidth for evolving regulations | Streamlines frameworks (NIST, ISO 27001) with automated tools |
| Incident Response | Slower containment (depends on internal teams) | Faster response via pre-negotiated playbooks and MSSP partnerships |
| Integration | Deeply embedded in company culture and decision-making | Objective perspective to identify blind spots |
| Ideal For | Large enterprises with complex security needs | SMBs with budget constraints, compliance needs, or evolving threats |

1. Discuss Scope
Let us know your requirement e.g. scope, duration, and deliverables.

2. Meet certified Security Company
Discuss your security project requirements, expectations, budget and goals.

3. Get Proposal, Blueprint & start
Choose your right cyber security company as per your budget and requirements to get started.
Simplifying Cyber Security Regulations complexity for UAE & GCC
Meet Effective vCISO Service Providers in USA per Security Budget Timeline Lean IT principles Security Program Compliance goals
Develop a security strategy for your organization, tied specifically to your risk priorities, regulatory compliance requirements, and the threat lands… through unique services offered by our vCISO (Virtual CISO) service Partners in the US
Risk Assessment & Management
Conduct comprehensive evaluations of IT infrastructure, applications, and processes to identify vulnerabilities, threats, and compliance gaps to protect the organization's assets.
- Perform vulnerability and threat analyses
- Prioritize risks based on impact and likelihood
- Targeted remediation measures
Security Strategy & Roadmap
Gain a customized security plan aligned with your goals, protecting your assets while optimizing resources.
- Design a 3-yr security roadmap with tech upgrades
- Prioritize risks for budget allocation
- Plan employee training to reduce vulnerabilities
Security Operations
Manage day-to-day security operations, including monitoring, incident response, and threat hunting.
- Use SIEM tools for real-time threat detection
- Respond to alerts with immediate action
- Hunt for hidden threats in logs
Security Architecture
Design and oversee the implementation of security architectures that protect the organization's networks and systems.
- Deploy zero-trust models for network security.
- Advise on firewall and encryption setups.
- Review architecture for scalability and protection
Managing the Information Security Team
Oversee the security team, providing guidance and ensuring alignment with security strategies.
- Guide IT on new control implementation
- Review team performance in incident response
- Assign tasks for ongoing security monitoring
Improved Security Awareness
Educate employees on cybersecurity best practices to reduce human error-related risks.
- Run phishing simulations to test staff awareness
- Provide training on social engineering tactics
- Distribute monthly security tips newsletters
Disaster Recovery
Develop and test disaster recovery plans to ensure business continuity in the event of a cyber incident.
- Set up daily automated backups for critical data
- Test recovery drills for system restoration
- Plan alternate operations during downtime
Creating Identity and Access Control Policies
Establish policies for managing user identities and access rights to protect sensitive data.
- Implement MFA for all employee logins
- Set RBAC to limit data access
- Monitor access logs for unauthorized attempts
Conducting Risk Assessments
Perform regular assessments to identify and evaluate cybersecurity risks, prioritizing mitigation efforts.
- Use threat modeling to assess system risks
- Identify vulnerabilities in third-party vendors
- Rank risks by impact for mitigation focus
Governance Frameworks
Develop and maintain policies, procedures, and governance structures aligned with standards like NIST, ISO 27001, HIPAA, or PCI-DSS.
- Perform vulnerability and threat analyses
- Prioritize risks based on impact and likelihood
- Targeted remediation measures
Compliance
Ensure the organization meets regulatory requirements and industry standards, such as GDPR, ISO 27001, HIPAA, or PCI DSS.
- Perform GDPR compliance audits annually.
- Prepare documentation for HIPAA certification
- PCI DSS payment security
Incident Response Management
Develop and manage plans for responding to security incidents, ensuring quick and effective mitigation of threats.
- Create ransomware response plans with containment steps
- Conduct post-incident analysis to improve defenses
- Coordinate with IT for rapid threat eradication
Contact us today for a personalized consultation!
Ready to Get a vCISO + MSSP team for less than the cost of a full-time IT manager?
Our services
vCISO Services with MSSP-Driven Value Enhancement
Risk Assessment & Management
Through our curated partner network, you gain a unified force of CISOs, SOC analysts, and compliance experts working as an extension of your team. Stop choosing between ‘big picture’ and ‘hands-on.’ With us, you get both.
24/7 SOCs
with <8-minute response SLAs
Cloud Security Specialists
for AWS/Azure/GCP
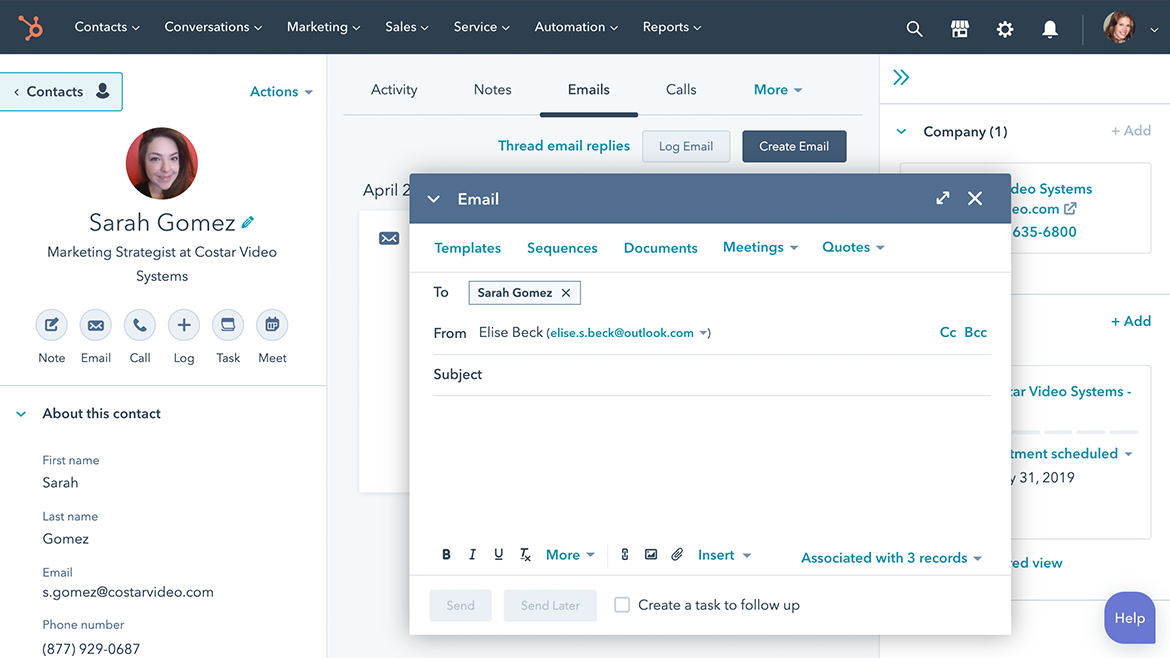
Social publishing
Sequences
Supercharge
Unify
Combine
Operational MSSP Services
24/7 Threat Monitoring
SIEM/SOAR with AI-driven anomaly detection
Endpoint & Cloud Defense
Managed EDR, zero-trust IAM, container security
Incident Response
Breach containment, forensic analysis, PR support
Incident Response
Breach containment, forensic analysis, PR support
Employee Training
Phishing simulations, compliance certifications
| vCISO Service | MSSP Service | Benefit for SMBs |
|---|---|---|
| Cybersecurity Strategy and Roadmapping | 24/7 SOC Monitoring | Ensures strategic alignment with continuous threat detection |
| Risk Management and Compliance | Compliance Governance and Audits | Meets regulatory requirements with expert oversight |
| Incident Response Planning | Incident Response and Analysis | Prepares for and responds to incidents effectively |
| Security Awareness and Training | Security Awareness Training (via MSSP) | Enhances employee awareness with operational support |
| Technology Selection and Implementation | Firewall and Antivirus Management | Implements cost-effective tools with expert management |
| Vendor Management | Managed VPNs and Third-Party Oversight | Ensures secure vendor integrations with operational support |
| Ongoing Monitoring and Support | Threat Intelligence and Analytics | Provides continuous oversight with advanced threat insights |
Get vCISO Service Provider
Ready to get started?
We hope to meet you soon
By combining the expertise of curated virtual Chief Information Security Officers (vCISOs) and a network of pre-vetted Managed Security Service Providers (MSSPs) , we bridge the gap between limited resources and evolving threats. Our team specializes in delivering tailored security strategies, compliance management, and 24/7 operational defense—without the cost of a full-time executive
(123) 456-7890
The vCISO Hiring process
01
Cost Savings
vCISO + MSSP avoids full-time salaries and tool investments
02
Scalability
MSSPs adjust services as threats evolve, avoiding overstaffing
03
Compliance
reduce audit prep time by 50%+
04
Resilience
MSSPs reduce breach impacts by 60% via proactive monitoring
Learn how the vCISO will strengthen SMB security posture efficiently and cost-effectively
- Initial Discovery & Stakeholder Alignment
- Gap Analysis & Risk Assessment
- Strategy Roadmap Presentation
- Cost-Benefit Discussion
- Next Steps & Collaboration
